The anatomy of Hibernate dirty checking
Introduction
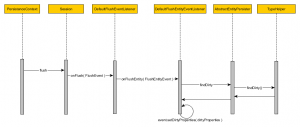
The persistence context enqueues entity state transitions that get translated to database statements upon flushing. For managed entities, Hibernate can auto-detect incoming changes and schedule SQL UPDATES on our behalf. This mechanism is called automatic dirty checking.
The default dirty checking strategy
By default Hibernate checks all managed entity properties. Every time an entity is loaded, Hibernate makes an additional copy of all entity property values. At flush time, every managed entity property is matched against the loading-time snapshot value:
So the number of individual dirty checks is given by the following formula:
where
n = The number of managed entities
p = The number of entities of a given entity
Even if only one property of a single entity has ever changed, Hibernate will still check all managed entities. For a large number of managed entities, the default dirty checking mechanism may have a significant CPU and memory footprint. Since the initial entity snapshot is held separately, the persistence context requires twice as much memory as all managed entities would normally occupy.
Bytecode instrumentation
A more efficient approach would be to mark dirty properties upon value changing. Analogue to the original deep comparison strategy, it’s good practice to decouple the domain model structures from the change detection logic. The automatic entity change detection mechanism is a cross-cutting concern, that can be woven either at build-time or at runtime.
The entity class can be appended with bytecode level instructions implementing the automatic dirty checking mechanism.
Weaving types
The bytecode enhancement can happen at:
- Build-timeAfter the hibernate entities are compiled, the build tool (e.g. ANT, Maven) will insert bytecode level instructions into each compiled entity class. Because the classes are enhanced at build-time, this process exhibits no extra runtime penalty. Testing can be done against enhanced class versions, so that the actual production code is validated before the project gets built.
- RuntimeThe runtime weaving can be done using:
- A Java agent, doing bytecode enhancement upon entity class loading
- A runtime container (e.g. Spring), using JDK Instrumentation support
Towards a default bytecode enhancement dirty checking
Hibernate 3 has been offering bytecode instrumentation through an ANT target but it never became mainstream and most Hibernate projects are still currently using the default deep comparison approach.
While other JPA providers (e.g. OpenJPA, DataNucleus) have been favouring the bytecode enhancement approach, Hibernate has only recently started moving in this direction, offering better build-time options and even custom dirty checking callbacks.
In my next post I’ll show you how you can customize the dirty checking mechanism with your own application specific strategy.
| Reference: | The anatomy of Hibernate dirty checking from our JCG partner Vlad Mihalcea at the Vlad Mihalcea’s Blog blog. |